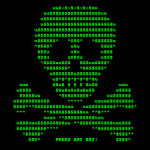
The latest ransomware outbreak dubbed “Petya” or “GoldenEye,” which experts feel originated, albeit unknowingly, from a supply chain vendor in the Ukraine or Russia, poses an unusual threat.
The latest ransomware outbreak dubbed “Petya” or “GoldenEye,” which experts feel originated, albeit unknowingly, from a supply chain vendor in the Ukraine or Russia, poses an unusual threat.
As was the case in a similar episode in May, the latest ransomware attack purportedly used attack code that is said to have originated from the U.S. National Security Agency and leveraged the same exploit, which uses a Windows Server Message Block flaw, to spread on networks. Microsoft had issued a “critical” security bulletin back in March to correct the flaw.
The counter-argument is that malicious software might still be embedded in Trojan-horse fashion on software distributed though the OS provider. WordPress, for one, has seen counterfeit plugins containing hacks posing as legitimate software and illicitly posted to its proprietary directories or Codex.
Lockscreen ransomware shows a full-screen message that prevents you from accessing your PC or files. It says you have to pay money (a “ransom”) to get access to your PC again.
Encryption ransomware changes your files so you can’t open them. It does this by encrypting the files – see the Details for enterprises section if you’re interested in the technologies and techniques we’ve seen.
Older versions of ransom usually claim you have done something illegal with your PC, and that you are being fined by a police force or government agency.
Ransomware can get on your PC from nearly any source that any other malware (including viruses) can come from. This includes:
- Visiting unsafe, suspicious, or fake websites.
- Opening emails and email attachments from people you don’t know, or that you weren’t expecting.
- Clicking on malicious or bad links in emails, Facebook, Twitter, and other social media posts, instant messenger chats, like Skype.
It can be very difficult to restore your PC after a ransomware attack – especially if it’s infected by encryption ransomware.
That’s why the best solution to ransomware is to be safe on the Internet and with emails and online chat:
- Don’t click on a link on a webpage, in an email, or in a chat message unless you absolutely trust the page or sender.
- If you’re ever unsure – don’t click it!
- Often fake emails and webpages have bad spelling, or just look unusual. Look out for strange spellings of company names (like “PayePal” instead of “PayPal”) or unusual spaces, symbols, or punctuation (like “iTunesCustomer Service” instead of “iTunes Customer Service”).

- Install and use an up-to-date antivirus solution (such as Microsoft Security Essentials).
- Make sure your software is up-to-date.
- Avoid clicking on links or opening attachments or emails from people you don’t know or companies you don’t do business with.
- Ensure you have smart screen (in Internet Explorer) turned on.
- Have a pop-up blocker running in your web browser.
- Regularly backup your important files.
The cardinal rule for all platforms is that, in a cloud based ecosystem, it is considered a best practice to perform daily backup files with a cloud storage service that keeps a history or archive of your files, such as Microsoft OneDrive which is now fully integrated into Windows 10 and Windows 8.1, and Microsoft Office or iCloud on the Apple platform. Dropbox, Box.com and SugarSync are other automated backup services that extend across multiple platforms. [24×7]