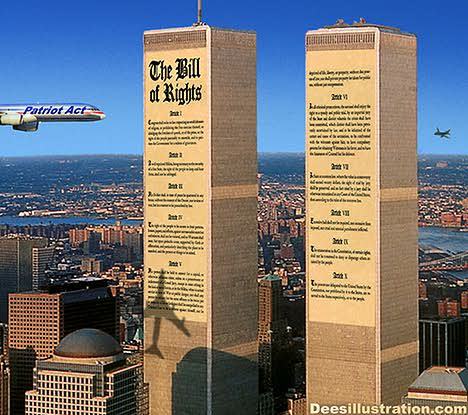
What was once a bright line illuminating First Amendment rights and freedom of expression for both the American free press and ordinary American citizens began to fade into darkness after the U.S. homeland was attacked on 9-11-2001.
Smoldering beneath the smoke and rubble of that catastrophic event was a burning ember that would ignite a sweeping transformation of our national security infrastructure.
Suddenly, the National Security Agency, or NSA, could not only connect the lines of every American citizen’s call history and personal contact network but blur the line as to how such information could be collected, from which sources, and how it could be used.
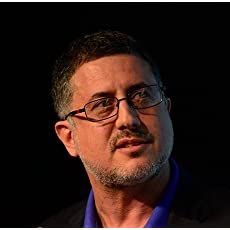
Journalist Barton Gellman was at ground zero when the Twin Towers were targeted. He had arrived back in New York City following a three-year assignment for the Washington Post as the newspaper’s bureau chief in Jerusalem. His reporting on the shock waves that emanated from the 9/11 bombing would win him a Pulitzer prize (the third such Pulitzer prize in his career).
What Bart could scarcely have imagined at that time is that just two years later a heavily encrypted message would pop-up on his computer screen with the download instructions for what amounted to the highly-classified surveillance playbook of the U.S. security establishment. The sender was an estranged intelligence officer, code-named Verax, who had made a furtive exit from a high-level NSA security post in Hawaii. The trove of highly classified documents in the download would effectively blow the lid off of what the informant purported was the existence of a national surveillance state.
Gellman had grown up with the Washington Post as a reporter and spent the larger part of his journalistic career there before departing in 2010. The incubator of such journalistic talent as (Bob) Woodward & (Carl) Bernstein, the Post had made investigative reporting a profession of rare distinction at the vanguard of the Fourth Estate. Bart returned there in 2013 as a freelance writer with the Verax documents in hand and found an extraordinary newsroom leader in executive editor Marty Baron. How he persuaded the Post to resume its vigilante vigor is as close as you can get to reality journalism, the opposite of what some might call “fake news.”
Today, roughly seven years after the first online rendezvous between Gellman and Verax, aka Edward Snowden, Gellman has produced a riveting account of the greatest, high stakes exposé in the history of American intelligence. Dark Mirror: Edward Snowden and the American Surveillance State recounts the opening moves, middle game tactics and endgame strategies of a virtual chess match with the world’s most wanted fugitive, how the deluge of top-secret documents Gellman decrypted was vetted for accuracy, how the revelations went from pixels to newsprint, and how the U.S. government was able to weigh-in, pre-publication on the most sensitive information.
Bart relates an origin story for the book that antedates Snowden. In 2011, the journalist was on the West coast sharing a stage in Silicon Valley with Google CEO Eric Schmidt. Schmidt asked him, “Wouldn’t you like to be able to say to your Android phone, ‘Where are my car keys?’”
“Good God, no,” Bart responded reflexively. “Maybe I’m in a casino. Maybe the bartender took my keys and I’m sleeping it off in a room upstairs, never mind whose. I’d be glad to have my phone track my life, but I don’t want you to know.”
Schmidt observed that Android users love the way their phones hand them information before they even ask. Bart could agree about the marvel of the technology, it was like having Batman’s Alfred in your pocket, except in this case Alfred was working for Google, not for Bart. Alfred could be following along, taking notes, but he is sending that data back to a company that may use it for personalized advertising or who knows what. Bart asked whether Schmidt could foresee a time when he might pay in cash for Google services, rather than agree to be spied on. The Google chief replied candidly. “That’s not our business model.” Until Snowden, it was (just about) nobody’s model.
The introduction to Snowden, alias Verax (Latin for “Truthteller”), came in the form of a referral from an old friend, filmmaker Laura Poitras. Snowden had also attempted contact with Glenn Greenwald of the UK’s Guardian but had not yet heard back. Gellman would be the first journalist in the world to report on Snowden’s travail.
Bart had written about classified matters plenty of times as a military and diplomatic correspondent. He was also vice president Dick Cheney’s biographer, author of the book titled Angler, after Cheney’s secret service codename. On a trip to Kitsap County in Washington state, he managed to hitch a ride on a nuclear submarine out of the Bangor base as a Pentagon reporter. His master’s thesis in college had long before parsed the political theory of “Secrecy, Security, and the Right to Know.” Until Snowden, he had never possessed the full text of a contemporary, codeword-classified document. Nobody had. Now he was contending with the most voluminous U.S. classified leak in history.
“WikiLeaks had published a quarter million diplomatic cables three years before,” Bart explained. “But those were classified Confidential or Secret. Nearly everything in this archive had Top Secret markings, most were “sensitive compartmented information,” or SCI, and many had cover names, handling caveats, and access controls that signified additional restrictions.
Scarcely Little Surveillance of COVID-19
If our cities, schools or churches were under threat of a concealed firearms attack then metal detectors would test every person seeking entrance. If there was radiation leak, a Geiger counter would measure who or what had been radiated. Yet, the idea of testing for a highly contagious disease agent seems somehow unnecessary and far-fetched?
The outbreak of a global pandemic has practically demanded that the U.S. government take a proactive role in “intelligence gathering” related to who may be infected by the virus, when and where, and their contact history. Yet this vital need has so far met with a feeble, ineffectual response. America’s death toll has already surpassed numbers that dwarf the tragedy of 9-11. At a time when gathering data by testing individuals could be life-saving, it is woefully deficient. Many employers and establishments now require body temperature checks, nasal swabbing, and contact tracing, yet such action by the federal government has been uncoordinated and unfunded. [24×7]
The USA PATRIOT Act was signed into law by U.S. President George W. Bush on October 26, 2001. The title of the Act stands for Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism Act of 2001.
But the real patriot act was that of Gellman taking action to process information that would safeguard the civil liberties of ordinary citizens and place a check on the unchecked power of the federal government Like the most spine-tingling spy novels, the book describes how each step along the gauntlet was fraught with peril and potential pitfalls. Only this was all too real.
According to Gellman, prior to their first meeting in person, Snowden wrote, “I understand that I will be made to suffer for my actions, and that the return of this information to the public marks my end.” Snowden also told Gellman that until the articles were published, the journalists working with him would also be at mortal risk from the United States Intelligence Community “if they think you are the single point of failure that could stop this disclosure and make them the sole owner of this information.”
The reportage revealed previously unknown details of a vast surveillance apparatus run by the NSA. The domestic surveillance did not spy on known terrorists. It aspired to cover substantially all Americans, collecting hundreds of billions of telephone and internet records, in the hope of discovering unknown conspirators.
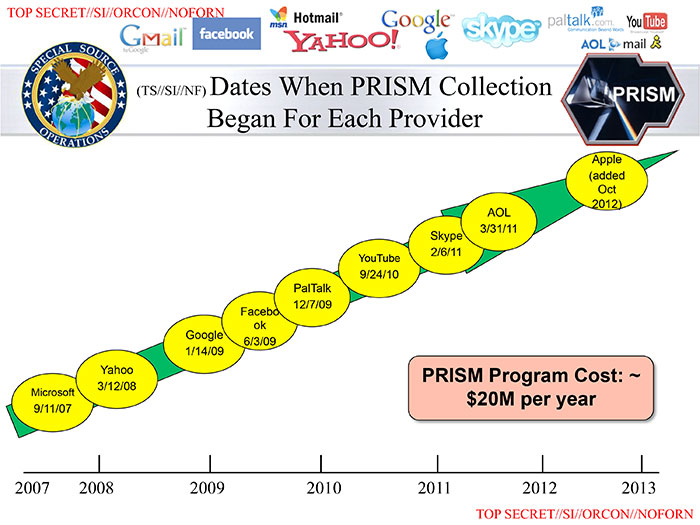
The first program to be revealed was PRISM, which allowed for court-approved direct access to Americans’ Google and Yahoo accounts
Gellman discloses in the book that one point of disagreement with the government was whether to include the names of outside companies that were involved. Gellman felt that naming the cohorts “would make it real to Americans.” The documents identified several technology companies as participants in the PRISM program, including Microsoft in 2007, Yahoo! in 2008, Google in 2009, Facebook in 2009, Paltalk in 2009, YouTube in 2010, AOL in 2011, Skype in 2011 and Apple in 2012.
The initial reporting also included details about an NSA call database, Boundless Informant, and of a secret court order requiring Verizon to hand the NSA millions of Americans’ phone records daily.
Like something out of a tragi-comedy, the NSA, the CIA and the UK’s GCHQ spied on the gamers of Second Life, Xbox Live and World of Warcraft, and attempted to recruit would-be informants from the sites, according to documents revealed in December 2013.
The NSA’s top-secret black budget, obtained from Snowden by The Washington Post, exposed the successes and failures of the 16 spy agencies comprising the U.S. intelligence community and revealed that the NSA was paying U.S. private tech companies for clandestine access to their communications networks. The agencies had been allotted $52 billion for the 2013 fiscal year.
Perhaps most devastating was the implementation of the dragnet, the revelation that the NSA was harvesting millions of email and instant messaging contact lists, searching email content, and tracking and mapping the location of cell phones, undermining attempts at encryption via software named Bullrun. The agency was using “cookies” to piggyback on the same tools used by Internet advertisers “to pinpoint targets for government hacking and to bolster surveillance.”
To be clear, “PRISM was not a mass surveillance program,” Gellman writes. “PRISM did not and could not scoop up Hotmail or Yahoo accounts in bulk. The NSA chose target accounts by way of individual taskings, the term of art. Analysts identified those accounts by email address or a comparably specific factor such as the telephone number used for registration. “
The acquisition of Americans’ content under PRISM was “incidental” to surveillance aimed at foreigners, but that did not mean it was unforeseen. The NSA kept all that data, and “minimizing” only restricted access to the U.S. identities. Many officials had authority to unmask them, in order to understand the intelligence in context or for other reasons.
Still, even the best-informed journalists and policy analysts had no information on the way PRISM worked. Plaintiffs could bring no constitutional challenge in federal court. Congress faced no public pressure, and big internet companies encountered little demand for stronger defense of privacy. Voters and consumers could not ask for change because they did not know the truth.
While not a defender of Snowden, Gellman believes that the whistle blower has done more good than harm and that he acted with the best of intentions for the public good.
By the letter of the statute, Snowden is already guilty of the draconian Espionage Act which makes no distinction for whistleblowers from foreign spies.
Nonetheless, Bart admits: “The Internet would be radically less secure today had it not been for Snowden. We would have much less of a picture as citizens between the boundary of the government and its constituents, between intelligence and a free society.”
“Because of Snowden,” he remarks, “the giants of the Internet, including Google and Facebook and Microsoft, have begun to encrypt all of their connections to your machine.”
Barton Gellman’s efforts in separating the wheat from the chaff and culling through silos of information to seek out what was most important for the public to know and for a publisher to withhold was a true patriot. His reporting played no small part in reducing the damage to our individual right to privacy that the original Patriot Act prescribed. [24×7]